Network Topology
Topology

Problem Description
The wireless AC uses the iMC as the radius server, and the iMC synchronizes ldap users to complete dot1x authentication.
Process Analysis
This authentication method involves wireless terminal dot1x settings, wireless device configuration, iMC configuration, ldap configuration, and the configuration is more complicated
Solution
1.AC side configuration:
radius scheme imc
primary authentication 172.16.1.71
primary accounting 172.16.1.71
key authentication simple h3c.com
key accounting simple h3c.com
user-name-format without-domain
nas-ip 192.168.1.4
#
domain imc-dot1x
authentication lan-access radius-scheme imc
authorization lan-access radius-scheme imc
accounting lan-access radius-scheme imc
#
wlan service-template 3
ssid hwzc-dot1x-imc
client forwarding-location ap
akm mode dot1x
cipher-suite ccmp
security-ie rsn
client-security authentication-mode dot1x
dot1x domain imc-dot1x
service-template enable
#
radius session-control enable
#
dot1x authentication-method eap
#
2.IMC side configuration
1) IMC docking with AC wireless service configuration.
Add access device, note that the shared key is the same as the radius scheme configuration key.

Add an access policy, select "EAP-PEAP" for the eap type, and "MSCHAPv2" for the subtype. Generally, Windows supports this method by default.

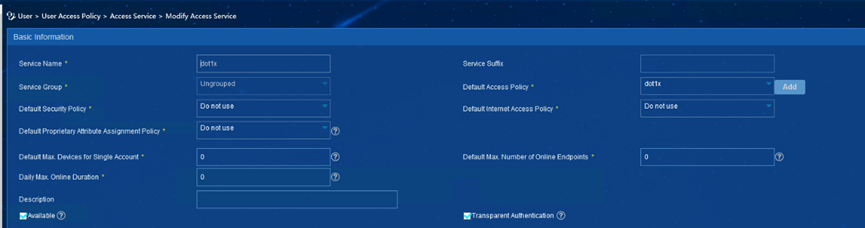
Select the access policy for the access service. The service suffix is the same as the " user-name-format without-domain " configuration on the command line.
In addition, dot1x wireless authentication requires CA certificate, import EAP root certificate and server certificate on this tab, import EAP root certificate.The test certificate can refer to the attachment.
Import EAP root certificate:

Import server certificate:

2) IMC connects to LDAP AD to synchronize user configuration.
On the AD server side, you need to confirm the distinguishedName of the Users account of the Administrator account. The DN number can be viewed through "View-Advanced Features-Users-Administrator Properties-Property Editor-distinguishedName".
Administrator account DN: CN=Administrator,CN=Users,DC=overseas,DC=com;
Common dot1x user DN: CN=Users,DC=overseas,DC=com.

Create a new virtual machine computer, name it "h3c", and click OK.

View the full computer name of the AD server: WIN-488845EQJ61.overseas.com

Create a new ldap server on the IMC, fill in the AD server IP address, enter the DN and password of the Administrator account, and enter the Base DN of the administrator account. Click test to test connectivity.

Advanced Information Check "MS-CHAPv2 Authentication", enter "AD server IP address", "Computer full name", "Virtual computer name h3c", set the virtual machine computer password to "h3c.com!"

Add ldap sync policy, "sub-base-dn" and "base-dn" are the same, click next.

Keep other information as default, check "dot1x service" for access service, and click Finish.

LDAP parameters Download the script to the AD server to edit and modify the name, domain name and password of the virtual computer.

Change CN to virtual computer name "h3c", DC to domain name "overseas", and virtual computer name to "h3c.com!"

AD server open cmd and enter the directory where the script is located, Execute the command "cscript ModifyComputerAccoutPass.vbs" to run the script to update the virtual computer password.

Finally, click Sync on the ldap policy to synchronize the ldap users to the IMC.


3. Business verification
1)The Windows terminal can use the built-in dot1x function: For the Windows terminal to enable the dot1x function, please refer to the case:https://knowledge.also3from.com/theme/details/166064
Connect the terminal to the ssid, enter the user name and password synchronized to the iMC on the ldap, and display that the SSID is connected.


See users online on IMC:

View the dot1x authentication session on the AC:

2) Connect the Huawei mobile phone to the SSID and enter the username and password. Shows the SSID is connected.


See users online on IMC:

3. Apple mobile phone connected to SSID, online successfully


See users online on IMC:

